Crayonic Device Manager
Executive Summary
Crayonic Device Manager (CDM) is an enterprise security platform for monitoring, managing, and auditing Crayonic devices — Crayonic Badge, Crayonic KeyVault, Crayonic Bridge — across Windows environments. It provides real-time security event monitoring, multi-tenant organization management, and audit capabilities for security administrators. CDM can be deployed on-premises or in the cloud (Azure / AWS / GCP or private cloud), and exposes a REST API for integration with SIEM tools and platforms such as Microsoft Entra ID, Microsoft Sentinel, and Microsoft Security Copilot.
Architecture Overview
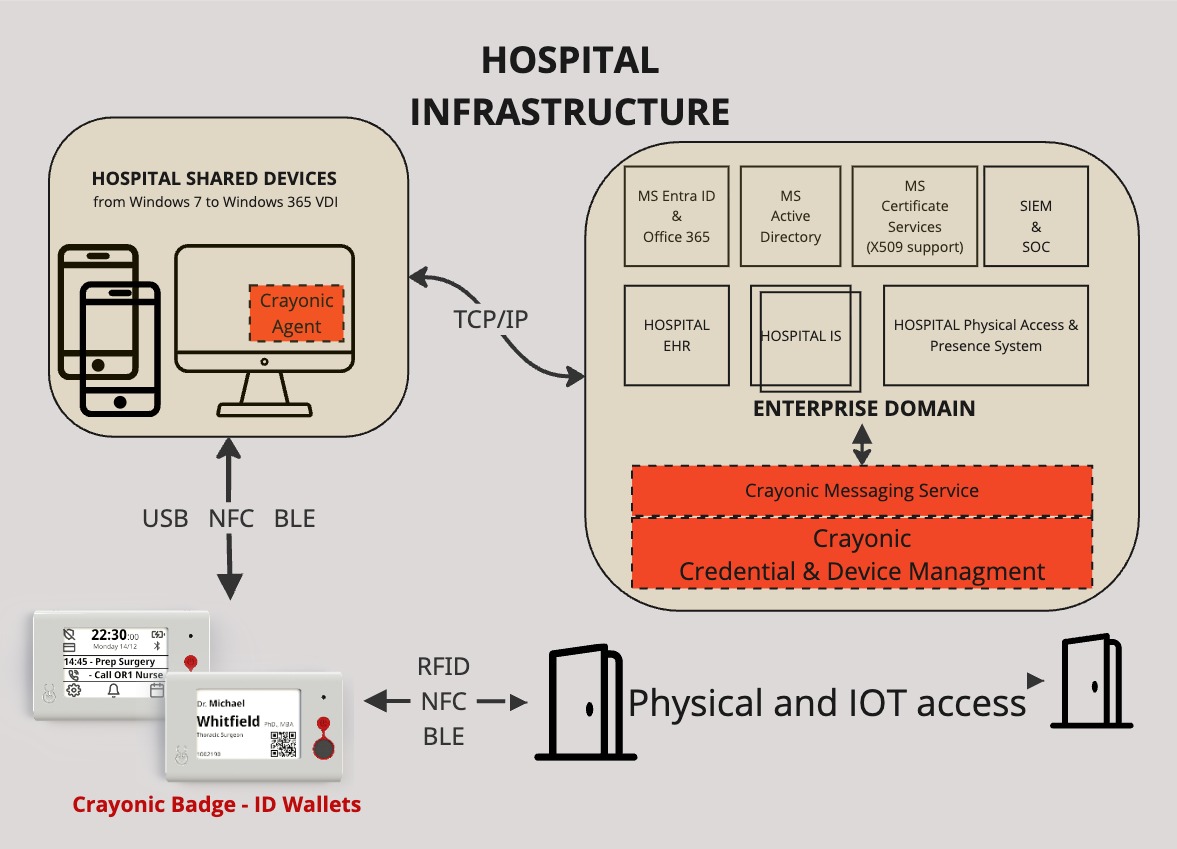
CDM follows a three-tier architecture:
- Crayonic Agent — Windows service deployed on each monitored machine
- REST API Backend — centralized data processing and management (Flask + MySQL)
- Web Administration Console — browser-based management interface (React)
┌─────────────────┐ ┌─────────────────┐ ┌─────────────────┐
│ Crayonic │ │ REST API │ │ Web Admin │
│ Agent │───▶│ Backend │◀───│ Console │
│ (Windows) │ │ (Flask/MySQL) │ │ (React) │
└─────────────────┘ └─────────────────┘ └─────────────────┘
For the endpoint side — installation, configuration, logs — see Crayonic Agent. This page covers the backend and console.
Core Security Features
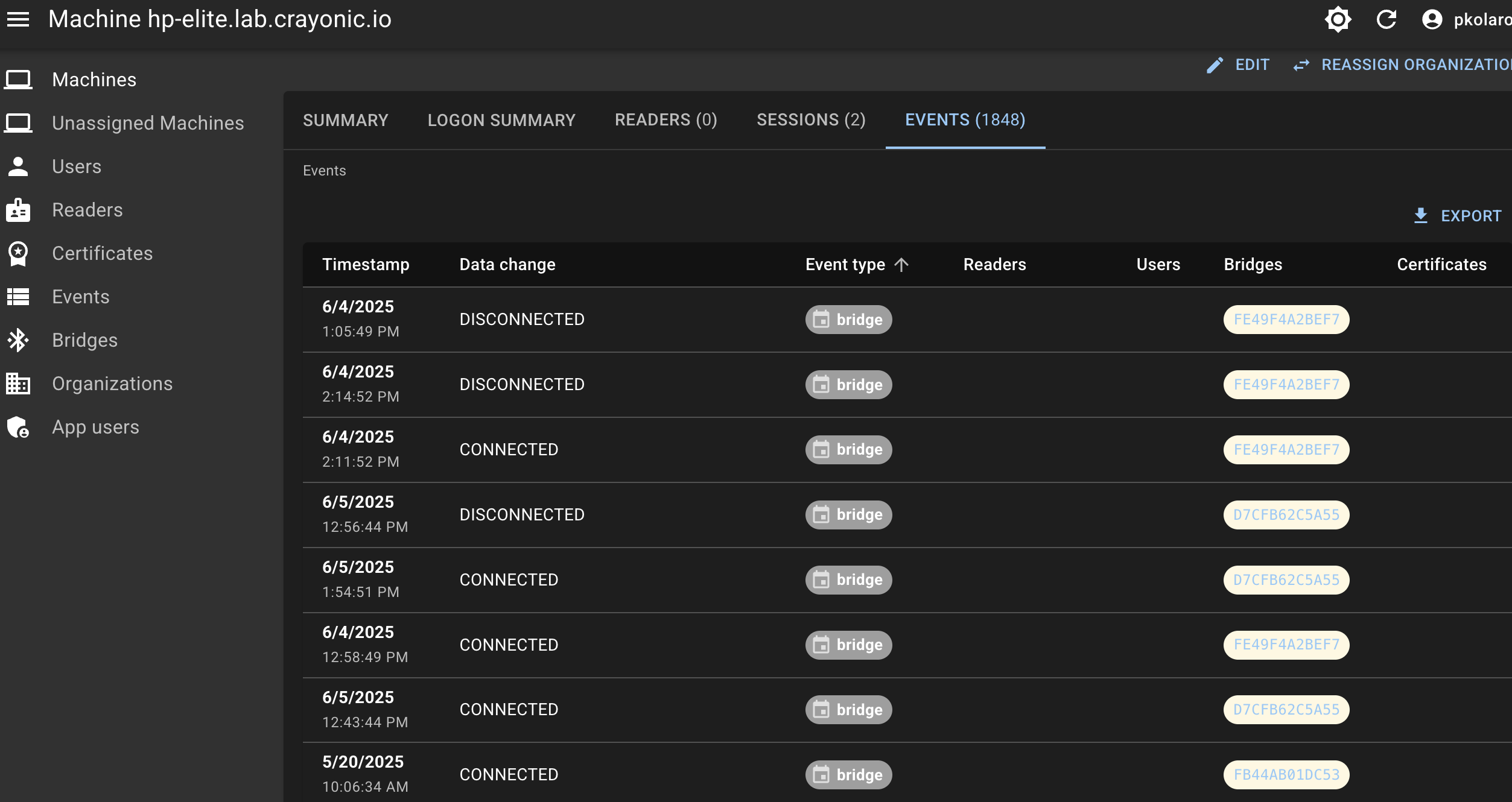
Real-Time Security Event Ingestion
CDM ingests and correlates the events produced by each Crayonic Agent:
- Authentication events — smart-card insertions and removals, PIV certificate authentications, FIDO2 / WebAuthn security-key operations
- Session events — logon, logoff, lock, unlock, session termination
- Device events — KeyVault and Badge connections, reader status changes, firmware updates, tampering indicators
- System events — agent health, network connectivity, service state
Advanced Capabilities
- Automatic workstation lock — configurable policy per organization; the Agent enforces on-endpoint, CDM records and reports
- Certificate management — discovery, expiration monitoring, integration with enterprise CAs, automated lifecycle
- Firmware management — signed updates pushed from CDM to Agents, with rollback and per-device version tracking
Multi-Tenant Organization Management
Isolation
- Complete data isolation — each organization sees only its own data
- Hierarchical access control — multiple administrative levels
- Cross-organization protection — prevents data leakage between tenants
- Scalable — unlimited organizations on a single instance
Role-Based Access Control (RBAC)
System-level roles
- Superadmin — global system access, org create/delete
- Admin — system-level access, user management
- User — standard system access
Organization-level roles
- org_admin — org administration, org user management
- org_user — standard org member access
- org_viewer — read-only
Security Boundaries
- Machine, event, user, and audit data are all scoped by organization membership.
Use Cases for Security Administrators
Compliance and Audit Management
- SOX — audit trails for financial system access
- HIPAA — healthcare data access monitoring
- PCI DSS — payment-card industry requirements
- GDPR — data access tracking and privacy controls
Audit capabilities: full event logging with timestamps and context, user activity tracking, device-usage reports, timeline reconstruction, exports for compliance reporting.
Incident Response and Forensics
- Real-time alerting
- Event correlation across machines, users and devices
- Timeline reconstruction
- User-behavior analysis
- Long-term historical trend identification
- Tamper-evident event storage
Access Control and Identity Management
- Privileged-access monitoring
- Certificate-based auth enforcement
- Multi-factor compliance tracking
- Session management
- Identity lifecycle (onboarding, reviews, offboarding, role changes)
Risk Management and Security Operations
- Anomaly detection on authentication patterns
- Unauthorized access attempt monitoring
- Device-tampering detection
- Policy violation detection
- Centralized policy deployment and automated remediation
Deployment
Backend and Console
- Cloud-ready — deploy on Azure, AWS, GCP, or private Kubernetes with auto-scaling
- High availability — redundant infrastructure with failover
- Secure APIs — REST with OAuth2 and JWT authentication
- Encrypted storage — data at rest encrypted with access controls
Enterprise Integration
- Active Directory — existing identity stores
- SIEM — export events to any SIEM platform
- Single Sign-On — OAuth2 / OIDC with Microsoft Entra ID and other providers
- Custom integrations — REST API for automation
Monitoring and Alerting
- Real-time dashboards and visualization
- Configurable alerts on event patterns
- Reporting engine for automated compliance and security reports
- Email, SMS and webhook notifications
Security and Privacy
Data Protection
- Encryption at rest — industry-standard algorithms
- Encryption in transit — TLS 1.3 for all network communication
- Access controls — RBAC with least privilege
- Retention — configurable retention policies
Privacy Controls
- Data minimization — only security-relevant data collected
- Anonymization — optional anonymization of personal identifiers
- Right to erasure — remove user data on request
- Consent management — granular consent for data collection
Getting Started
Prerequisites
- Windows 10 / 11 workstations with the Crayonic Agent installed
- MySQL 8.0+ (or compatible) for the backend
- Modern web browser for the admin console
- Network connectivity between agents and the central backend
Deployment Steps
- Stand up the backend service and database.
- Install the Crayonic Agent on each monitored workstation.
- Configure organizations and assign user roles.
- Assign machines to organizations.
- Configure security policies and alerting rules.
Event Types and Sample Payloads
User Session Event
{
"event_type": "user",
"change": "WTS_SESSION_LOGON",
"session_info": {
"UserName": "john.doe",
"LogonDomain": "ENTERPRISE",
"SessionId": 1,
"State": "Active"
},
"workstation_locked": false,
"timestamp": 1704067200
}
Device Connection Event
{
"event_type": "reader",
"change": "PLUGGED_IN",
"device_id": "CRAY-KV-001234",
"device_info": {
"firmware_version": "1.2.3",
"hardware_version": "2.1",
"battery_level": 85,
"interface_type": "PIV"
},
"timestamp": 1704067200
}
Certificate Event
{
"event_type": "certificate",
"change": "CERTIFICATE_DETECTED",
"certificate_info": {
"serial_number": "1A2B3C4D5E6F",
"issuer": "Enterprise CA",
"subject": "CN=John Doe,OU=IT,O=Enterprise",
"upn": "john.doe@enterprise.com",
"expiration": "2025-12-31"
},
"timestamp": 1704067200
}
API Reference
Authentication
POST /auth/login
POST /auth/logout
POST /auth/refresh
GET /auth/token
Organizations
GET /organizations
POST /organizations
PUT /organizations/{id}
DELETE /organizations/{id}
GET /organizations/{id}/users
POST /organizations/{id}/users
Events
GET /events
GET /events/{id}
GET /machines/{id}/events
GET /users/{id}/events
POST /events/search
Devices / Machines
GET /machines
GET /machines/{id}
PUT /machines/{id}
GET /machines/unassigned
POST /machines/{id}/assign-organization
Integration Examples
PowerShell
$headers = @{
'Authorization' = "Bearer $token"
'Content-Type' = 'application/json'
}
$events = Invoke-RestMethod -Uri "https://api.example.com/events" `
-Headers $headers -Method GET
$authEvents = $events | Where-Object {
$_.event_type -eq "user" -and
$_.data.change -like "*LOGON*"
}
SIEM Forwarding (Python)
import requests
def export_security_events(start_time, end_time, api_token):
headers = {
'Authorization': f'Bearer {api_token}',
'Content-Type': 'application/json',
}
params = {
'start_time': start_time,
'end_time': end_time,
'event_type': 'security',
}
r = requests.get('https://api.example.com/events', headers=headers, params=params)
return r.json()
Troubleshooting
Agent Connectivity
- Symptom — Agents not reporting events.
- Action — check network connectivity, firewall rules, certificate validity. Inspect agent logs via Windows Event Viewer. See Crayonic Agent.
Authentication Failures
- Symptom — users cannot access the web console.
- Action — verify OAuth2 configuration and the user's org assignments. Check JWT validity and user permissions.
Performance
- Index timestamp and organization_id columns.
- Apply appropriate event retention.
- Monitor CPU and memory on endpoints running the Agent.
Maintenance
- Database cleanup — purge events per retention policy
- Certificate renewal — rotate TLS certificates before expiry
- Agent updates — rolling updates via Crayonic Agent's auto-update mechanism
- Backups — verify DB backups and recovery procedures
- Access reviews — quarterly review of users and permissions
- Vulnerability scanning — regular infrastructure scans
- Penetration testing — annual assessment
- Compliance audits — periodic verification